On September 29, 2020, the Department of Defense (DOD) issued an interim rule (Assessing Contractor Implementation of Cybersecurity Requirements (DFARS Case 2019-D041)) implementing two separate requirements for defense contractors related to cybersecurity that change acquisition. The two requirements give contractors much-needed clarity around how to prioritize their efforts to improve cybersecurity in alignment with DOD acquisition. The DFARS interim rule provides timelines and scoping information related to the Cybersecurity Maturity Model Certification (CMMC) implementation, enabling contractors to plan and implement against those requirements accordingly. In priority order and plain English here are both the new requirements and what your company should be doing now; for a deeper look at the 89-page rule please read our FAQ.
What You Should Do Immediately to Address the DFARS Interim Rule
Let’s start with the answer; get compliant with NIST 800-171 by implementing all the security requirements defined within that publication. Immediately actionable is the requirement to submit your NIST 800-171 assessment, using the DOD approved scoring methodology, through the Supplier Performance Risk System (SPRS).
First, understand that this interim rule immediately impacts all of your future DOD awards if they include DFARS 252.204-7012 Safeguarding Covered Defense Information and Cyber Incident Reporting. This includes contracts, task orders, options, etc. Below is the language directly from the DFARS Interim Rule as to scope and impact for anyone who thinks this does not apply to them:
“The contracting officer shall verify that the summary level score of a current NIST SP 800-171 DOD Assessment (i.e., not more than three years old, unless a lesser time is specified in the solicitation) (see 252.204-7019) for each covered contractor information system that is relevant to an offer, contract, task order, or delivery order are posted in Supplier Performance Risk System (SPRS), prior to:
(1) Awarding a contract, task order, or delivery order to an offeror or contractor that is required to implement NIST SP 800-171 in accordance with the clause at 252.204-7012; or
(2) Exercising an option period or extending the period of performance on a contract, task order, or delivery order with a contractor that is required to implement the NIST SP 800-171 in accordance with the clause at 252.204-7012.”
Ideally, you will submit your scored assessment within the next 60 days but at a minimum, it is required before your next expected DOD contract award so timing is unique to each company. Information that you are required to share and enter with the results of your Basic NIST SP 800-171 DOD Assessment into SPRS includes:
- Date of the assessment
- Summary level score (e.g., 95 out of 110, NOT the individual value for each requirement)
- Scope of the Basic Assessment – identify each system security plan (security requirement 3.12.4) supporting the performance of this contract. All company CAGE codes must be mapped to the appropriate system security plan(s). Additionally, a brief description of the planned architecture may be required, if more than one plan exists
- Plan of Action Completion Date – a date that a score of 110 is expected to be achieved for each system security plan assessed (i.e., all requirements implemented) based on information gathered from the associated plan(s) of action developed in accordance with NIST SP 800-171 (security requirement 3.12.2)
Why You Should Immediately Address these Aspects of the Interim Rule
Given the level of information that you are required to expose to the government contractors should have a sense of urgency around getting started with NIST 800-171 compliance if they have not already. If you score poorly it’s doubtful that your general counsel, contracts, or other business partners will want a substandard assessment sitting in a government database potentially putting you at a competitive disadvantage. Scoring can range from +110 (Perfect) to -203 (Failure), so you will want to use these next 60 days to make improvements and produce the best score possible before you submit your assessment.
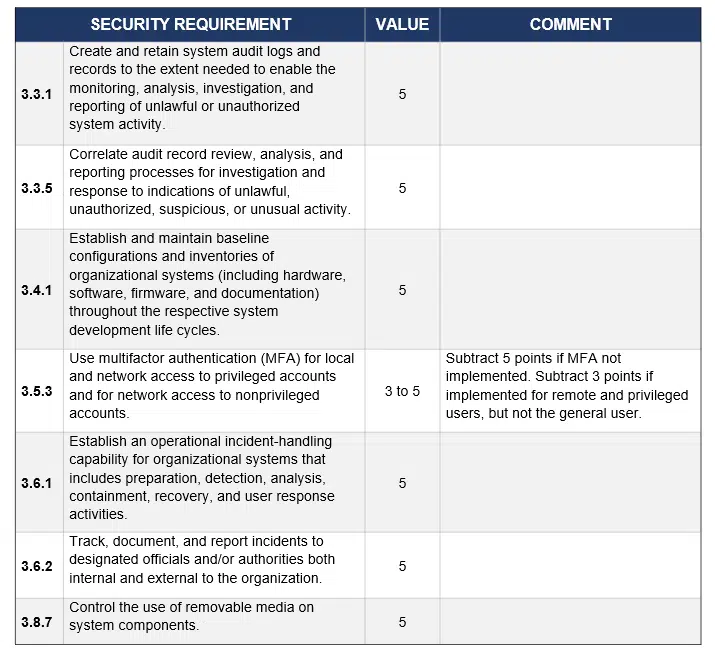
Scoring for Basic, Medium, and High NIST SP 800-171 DOD Assessments is the same. The scoring methodology security requirements are weighted so just looking at some of the highest weighted requirements can give you a sense of how much work you might have ahead of you. If you are responsible for NIST 800-171 compliance at your company it’s easy to quickly determine how bad, or good, you might fare by looking at the scoring methodology and comparing that to what you are, or are not, doing today. Of the hundreds of assessments CyberSheath has done over the last eight years we have observed, on average, 70% non-compliance. Take a quick look at these requirements and associated values and compare them against what you know to be true for your organization, did you just lose 35 points before you even started your assessment?
These are just 7 of the 110 security requirements but they all require hard work and dedicated resources to become compliant. Again, this represents only 35 of 110 possible points so hopefully, our point is clear, implementing these security requirements takes time. The DFARS Interim rule represents an emergency for non-compliant DOD contractors.
For almost two years now, we’ve been telling clients that their focus is and should always have been on NIST 800-171 compliance, as mandated in DFARS clause 252.204-7012. Now the DOD is clamping down on non-compliance.
Next Steps
Sprint to compliance in less than 60 days with CyberSheath’s proven methodology based on three core disciplines: Assess, Implement, Manage (AIM™)