We are a certified, specialized cybersecurity compliance service provider with a long track record of helping our customers with NIST SP 800-171, DFARS and CMMC 2.0 beginning-to-end cybersecurity services and solutions.
We will tell you exactly what you need.
Then, we’ll deliver it. All of it.
NOW AVAILABLE:
State of the Defense Industrial Base Report
We’re CMMC/DFARS experts.
We helped write the rules.
We’ll help you follow them.
Our executives have been involved in the development of every major cybersecurity initiative since 2008.
We have completed hundreds of NIST 800-171
assessments and implementations for our clients, and we are a certified CMMC 2.0 Level 2 service provider.
Expertise. Experience. Results.
1,000s
Level 2 Certified
100%
25%
99%
78+

We solve the whole problem.
We are one of the industry’s few one-stop providers.
We apply our three-stage AIMTM process —
Assess, Implement, Manage — to achieve and
maintain full compliance with all applicable DOD
requirements, at the appropriate level, with a
minimum amount of pain.
It’s about compliance.
Not just software.
Be careful when talking to
software-first providers.
Selling Microsoft GCC licenses is how
many value-added resellers (VARs)
make their money, which can increase
your chance of overpaying to under-
comply. How do you identify a software-
first provider?

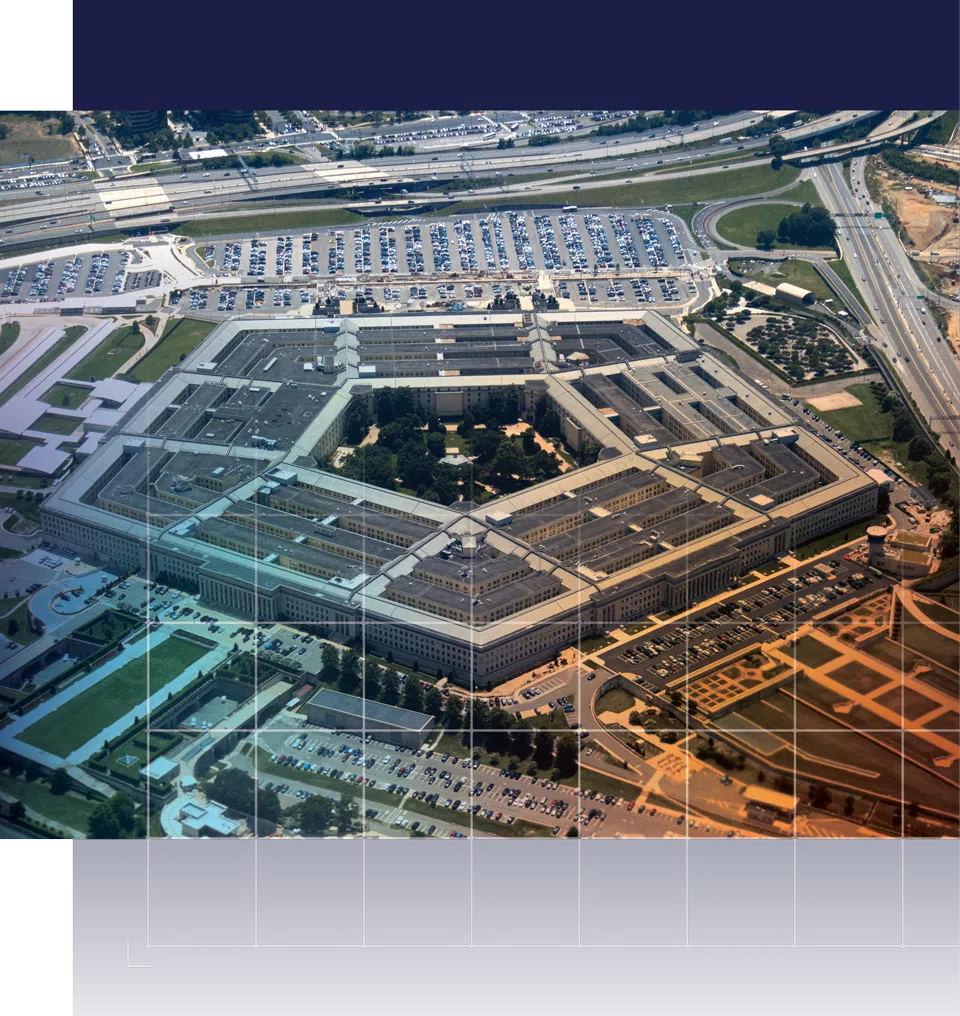
Get CMMC 2.0 compliant.
CMMC 2.0 noncompliance is a deal breaker for DOD contracts.
The DOD is now including CMMC 2.0 compliance requirements in the vast majority of RFIs, RFQs, RFPs, and contracts. Protect your business and your employees. Get compliant.
Federal Enclave: Achieve compliance without rebuilding your entire environment.
For organizations that support both DOD and commercial customers, CyberSheath’s Federal Enclave provides a purpose-built, cloud-based compliant environment to securely handle DOD project data. Designed to meet NIST SP 800-171, DFARS and CMMC 2.0 requirements, it enables contractors to isolate Controlled Unclassified Information without overhauling legacy infrastructure. The enclave can be deployed rapidly, helping organizations maintain eligibility for new contract awards, recompetes, and extension years.
Information. Insights. Knowledge.
Case Studies
Read stories about how your peers are achieving CMMC Level 2 compliance with CyberSheath support.
Browse Here >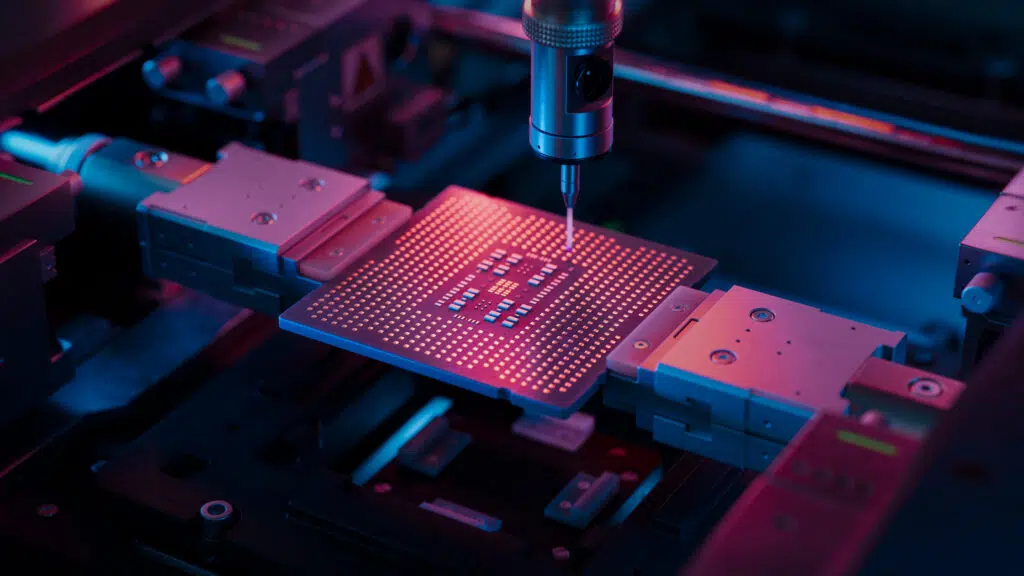
Spirit Electronics Case Study
Spirit Electronics is a vertically integrated electronics design and manufacturing solutions provider headquartered in Phoenix, Arizona. Spirit serves the military-aerospace markets with capabilities spanning ASIC design, post-foundry services, advanced packaging, screening and qualification, and onshore…
Learn MoreWebinars
Learn from CyberSheath experts about how to get CMMC compliant and avoid the pitfalls.
Browse Here >
Getting CMMC Scope Right the First Time
Avoid costly rework, failed assumptions, and surprise reassessments. Choosing your CMMC scope isn’t just a technical decision—it’s the foundation that determines your timeline, cost, and long-term success. Many organizations take the “easy button” approach, only…
Learn MoreBlogs
Gain useful insights and information on the processes and challenges of CMMC compliance.
Browse Here >
How to Achieve CMMC Compliance: 7 Essential Tips for Organizations
Many organizations pursuing CMMC certification make the same costly mistake: they start implementing security controls before they fully understand their scope. They purchase tools, migrate platforms, or build segregated enclave environments without first mapping where…
Learn MoreEvery solution begins with a conversation.
Contact our experts today for a no-obligation discussion of CMMC 2.0 compliance, what’s required, what you may need and what we can do to provide it. We’ve helped hundreds of DOD contractors. We can help you.